Introduction: Why Email Security Is Mission-Critical for Every Business
Email is the central nervous system of modern business. Contracts are signed, invoices are approved, confidential data is shared — all through inboxes.
But that convenience comes with massive risk.
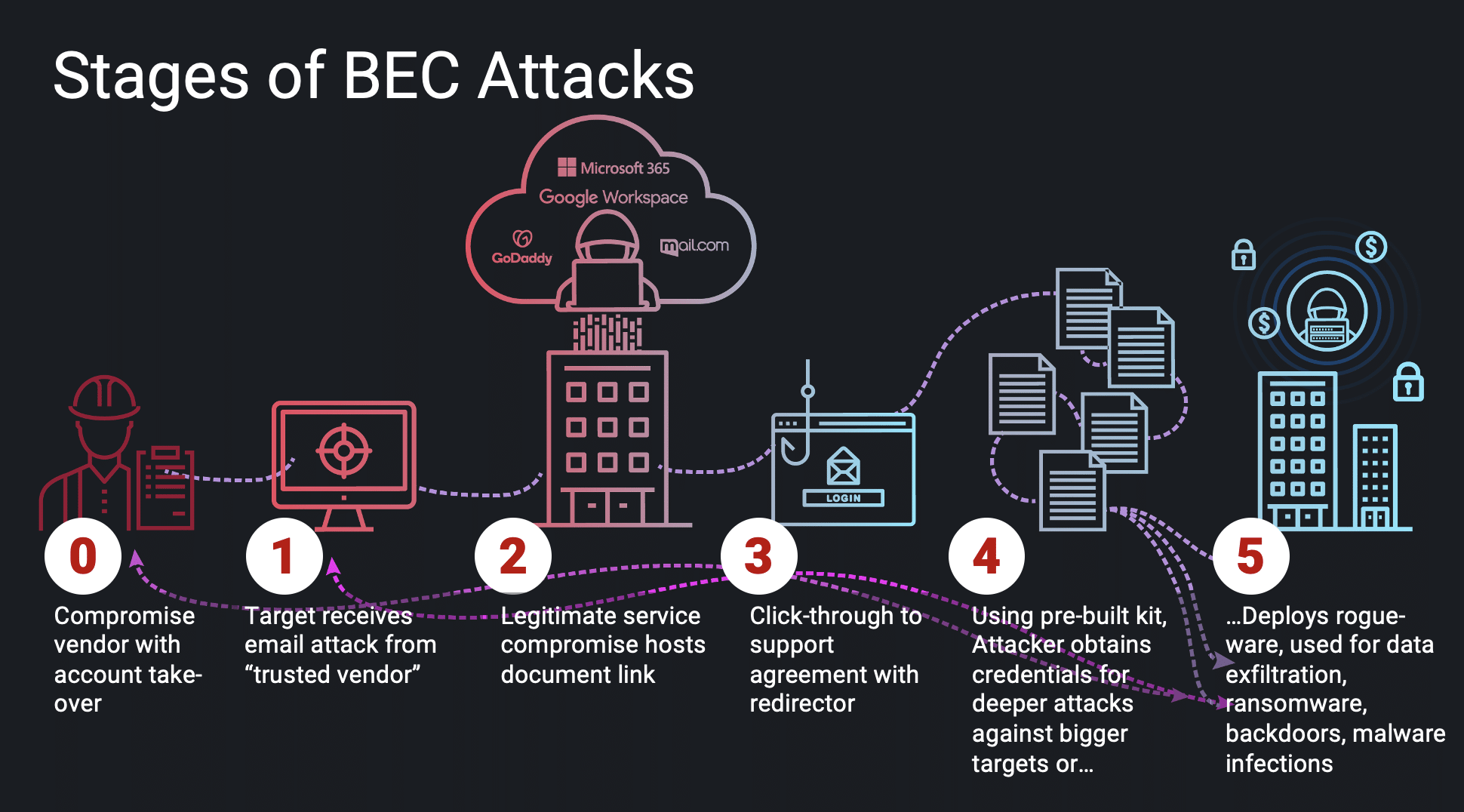
Today, cybercriminals don’t just “hack” networks — they manipulate people through email impersonation, phishing, and social engineering to breach systems and steal money or sensitive information. These targeted attacks are known as Business Email Compromise (BEC).
And they work. Alarmingly well.
Fact: The FBI reports over $50 billion lost globally due to BEC in the past decade — and SMBs are often the easiest targets.

Understanding BEC: What Makes It So Dangerous?
Business Email Compromise (BEC) involves attackers impersonating key stakeholders — such as a company’s CEO, accountant, or vendor — to deceive employees or clients into:
- Sending payments to fraudulent accounts
- Downloading malicious files
- Clicking fake invoice links
- Updating supplier bank details
- Sharing credentials or client data
Unlike traditional spam, BEC emails are often personalized, urgent, and look legitimate — making them difficult to spot.
Example: An attacker spoofed a Toronto-based CEO’s email domain by replacing an “m” with “rn” — tricking the CFO into wiring $22,000.
Also Read : Role of Managed IT Services in Swift Bug Detection
Top 5 Email Security Practices to Stop BEC Attacks
Let’s dive into real-world-proven email security strategies used by companies across Canada, the US, and the UK to stop compromise before it starts.
Enforce Multi-Factor Authentication (MFA) on Every Email Account
Passwords alone are no longer enough.
Even a strong password can be phished or leaked in a breach.
MFA makes it exponentially harder for attackers by requiring a second step — such as a code from an app, biometric scan, or USB token.
Enforce MFA for:
- C-suite email accounts
- IT admins
- Finance and HR departments
- Any user accessing emails remotely
Insight: A logistics company in Calgary blocked 11 unauthorized login attempts from overseas thanks to time-based MFA alerts.
Train Employees to Recognize and Report Phishing
Human error is the #1 cause of BEC success.
Even the best filters can’t stop an employee from clicking a convincing fake.
Training tips:
- Send fake phishing emails monthly to test awareness
- Teach employees to hover over links before clicking
- Show examples of real-world BEC attacks in their industry
- Promote a “report suspicious email” button in every inbox
Pro Trick: Run “spot the fake email” games during lunch & learns to boost engagement.
Stat: Employees who complete phishing simulations are 80% less likely to fall for real scams.
Use Advanced Email Filtering and Threat Protection Tools
Basic spam filters only catch generic threats. Today’s attackers use:
- Geo-targeting
- Business jargon
- Previous conversation threads
- Lookalike domains
Tools that can help:
- Microsoft Defender for Office 365 – Real-time AI-driven protection
- Mimecast – URL rewriting + attachment sandboxing
- Proofpoint – Identity-based filtering and DLP
- Google Workspace Enhanced Security – Context-aware access control
Case Study: A real estate agency in Vancouver avoided a $10,000 ransomware payout when Mimecast stopped a malicious PDF posing as a “buyer form.”
Configure SPF, DKIM, and DMARC to Protect Your Domain
Attackers often spoof your domain to pretend to be you.
This is where DNS authentication comes in.
| Record | Role |
| SPF | Authorizes specific servers to send email on your behalf |
| DKIM | Attaches a cryptographic signature to ensure email integrity |
| DMARC | Tells inboxes what to do if SPF/DKIM checks fail (e.g., reject or quarantine) |
Fact: Domains without proper SPF/DKIM/DMARC records are 25x more likely to be spoofed.
GoGeekz configures this for all managed clients — with regular reports on spoofing attempts blocked.
Audit & Monitor Email Activity Proactively
Security doesn’t end with setup. You need ongoing visibility.
What to monitor:
- Logins from unusual locations or devices
- Sudden email forwarding rules or mailbox delegation
- Mass sends to unknown contacts
- Failed MFA attempts or blocked phishing links
- Activity on shared or group inboxes
Example: A healthcare provider in Montreal caught a rogue admin mailbox auto-forwarding patient data using GoGeekz’s 24/7 email audit alerts.
Read More : Essential Cloud Security Practices for a Smooth Migration

Real-Life Scenario: Disaster Averted
An e-commerce company in Mississauga received an email from their “supplier” asking to update banking info.
Red flags:
- Email looked 99% legit
- The bank was in a new country
- It came during a holiday rush
Thankfully, their finance manager paused — and flagged the email.
Behind the scenes, GoGeekz’s email protection flagged it as:
- A lookalike domain (1 letter off)
- Unverified SPF
- Unusual sending location
No money was lost. But without email security awareness AND filtering, it could’ve been a $25,000 hit.
Bonus: Mistakes to Avoid
| Mistake | What Happens |
| No MFA on VIP accounts | C-suite gets phished first |
| Using personal Gmail for business | No audit trail, zero visibility |
| Ignoring email alerts | Attacks go undetected |
| Public Wi-Fi + unencrypted email | Risk of packet sniffing |
| Shared email passwords | Accountability is gone |
Secure vs. Insecure Email Practices
| Feature | Insecure | Secure |
| Access | Password-only | MFA enforced |
| Domain Control | No SPF/DKIM | All DNS records active |
| Awareness | No training | Quarterly simulations |
| Monitoring | None | Log-based alerts & AI analysis |
| Response | Reactive | Automated quarantine & threat response |
Myth vs. Fact
| Myth | Reality |
| “We use Outlook, we’re protected.” | Only if security is configured correctly |
| “Our staff would never fall for phishing.” | Even IT pros have clicked malicious links |
| “I don’t need email security as a startup.” | 43% of cyberattacks target SMBs and startups |
Real-World Story: When Compliance Meets Security
Let’s rewind to a growing law firm based in Toronto, Canada. Their reputation relied heavily on client trust and handling sensitive case files through email. They recently onboarded a high-profile client from London, UK, with strict GDPR compliance requirements.
The firm used basic spam filters and never heard of SPF or DMARC.
During onboarding, a spoofed email came through, requesting sensitive case data “urgently.” Thankfully, the junior associate paused and escalated it. But it was a close call.
Here’s what GoGeekz did next:
- Configured SPF, DKIM, and DMARC for their domain
- Enforced MFA for all team members
- Integrated advanced email filtering
- Conducted GDPR and PIPEDA-focused awareness training
- Added audit logs and alerts for cross-border communication
Today, whether emailing clients in Canada, the US, or the UK, their firm is fully compliant — and confidently protected.
Security isn’t just about tech. It’s about trust — across borders.
Conclusion
You don’t need to be a large enterprise to take email security seriously.
In fact, SMBs are the most frequent victims of BEC — and often the least prepared.
With GoGeekz Email Security Solutions, we help you secure inboxes, authenticate domains, train employees, and monitor suspicious activity — 24/7.
✅ Ready to lock down your inbox?
👉 Book your FREE Email Security Audit with GoGeekz today
We’ll help you identify weaknesses, patch gaps, and prevent the next BEC attempt before it starts.
FAQs
Industry Experiences
Innovative services for your business
We’re dedicated to making your businesses reliable, efficient, and safe.
We’re a one-stop solution for everything IT you need. Whatever you need, we got you covered:
Microsoft Defender or Google Workspace Enhanced Security.
No. You need user training, authentication records, and real-time monitoring.
Your reputation suffers, and you may lose clients. DMARC enforcement stops this.
Yes — we provide free security audits and setup reviews.
Not necessary. Use sandboxing and AI-based filters instead to avoid productivity loss.




